GitLab - OIDC
To use GitLab as an IdP to authenticate the Akeyless Platform by way of OIDC, follow the steps below.
Create an Application
-
In your GitLab account, go to Edit profile > Applications.
-
For Redirect URI set
https://auth.akeyless.io/oidc/callback, select the "openid", “profile” and “email“ scope and click Save application.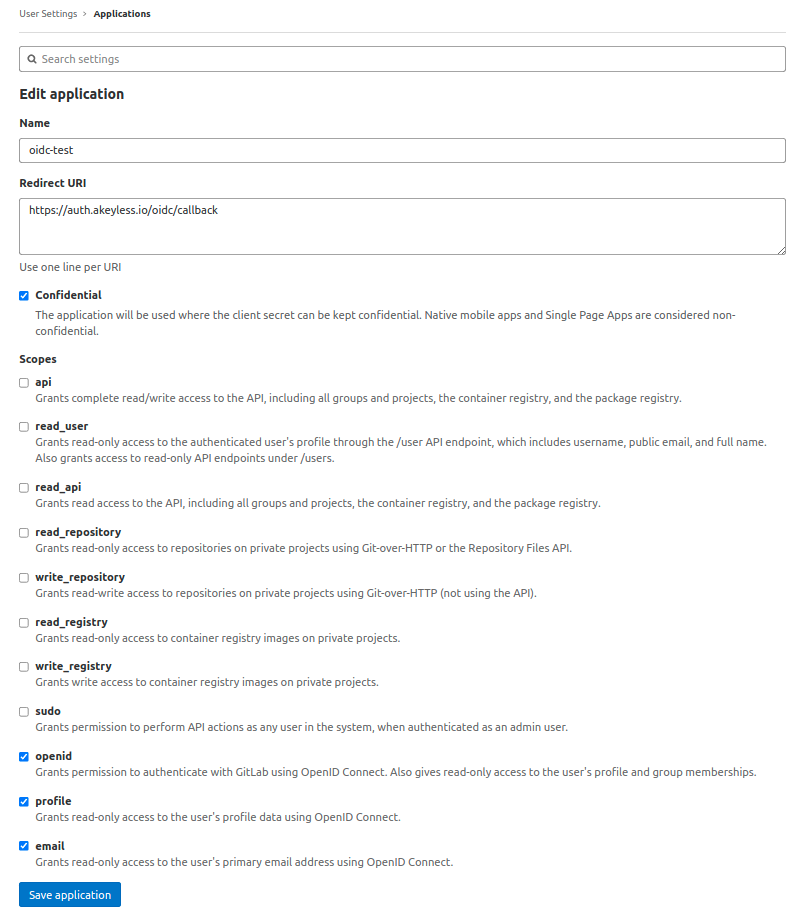
-
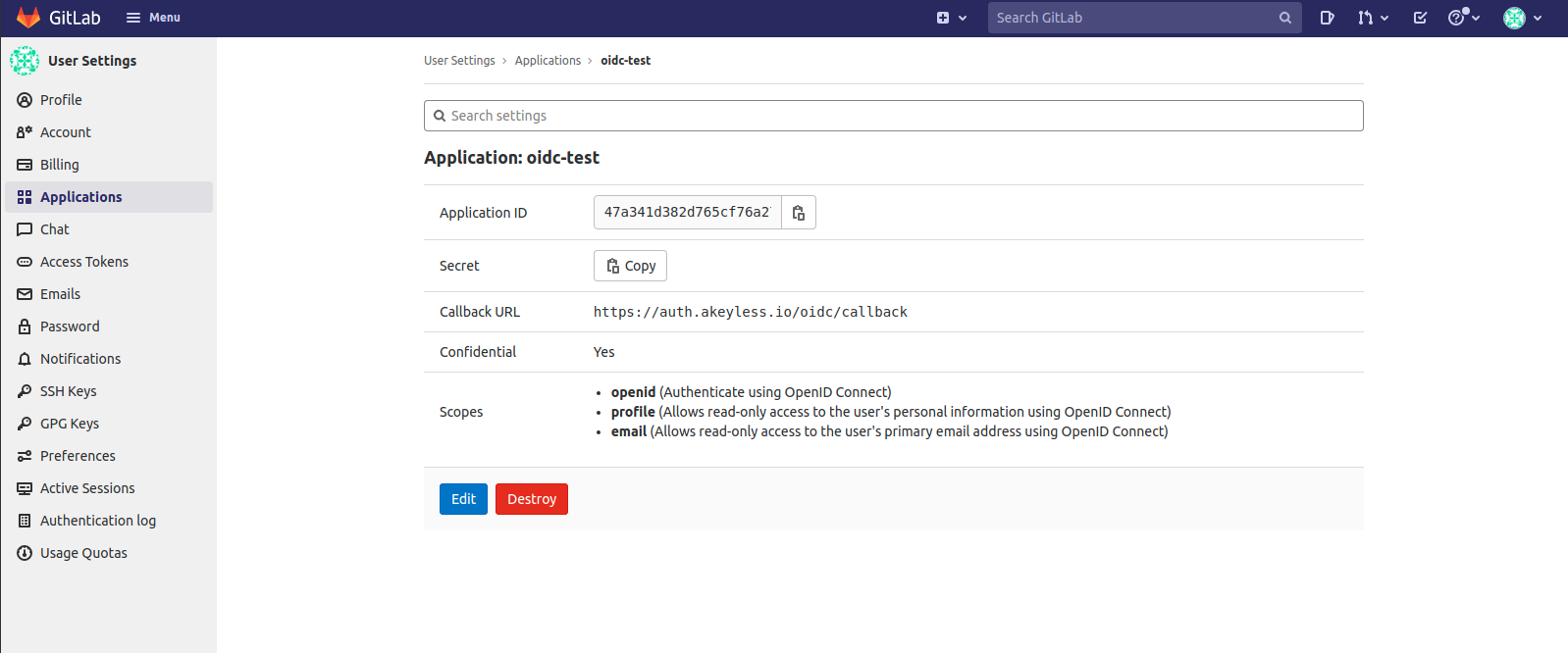
Once the application has been created, you need to obtain the Client ID and Client secret:
-
To bind the GitLab Client ID with your Akeyless account, create an OIDC Authentication Method using either CLI or UI, as described below.
Create an OIDC Authentication Method with the CLI
akeyless auth-method create oidc --name 'my GitLab app' --issuer https://gitlab.com --client-id {your-client-id} --client-secret {your-client-secret} --unique-identifier {your-unique-identifier (for example, 'email' or 'username')}Log in With OIDC Using the CLI
-
Configure a new profile with your Access ID from the previous step and OIDC type (if no profile name is provided, the default will be configured):
akeyless configure --access-id <your-access-id> --access-type oidc --profile 'gitlab-oidc' -
Now, you can run any Akeyless CLI command and be authenticated with GitLab:
akeyless list-items --profile gitlab-oidc
Updated 3 months ago
