Targets
A target is a reusable endpoint credential item for a database, cloud platform, or server. Targets help admins keep endpoint details organized so you can reuse them across secrets instead of entering the same information for each item.
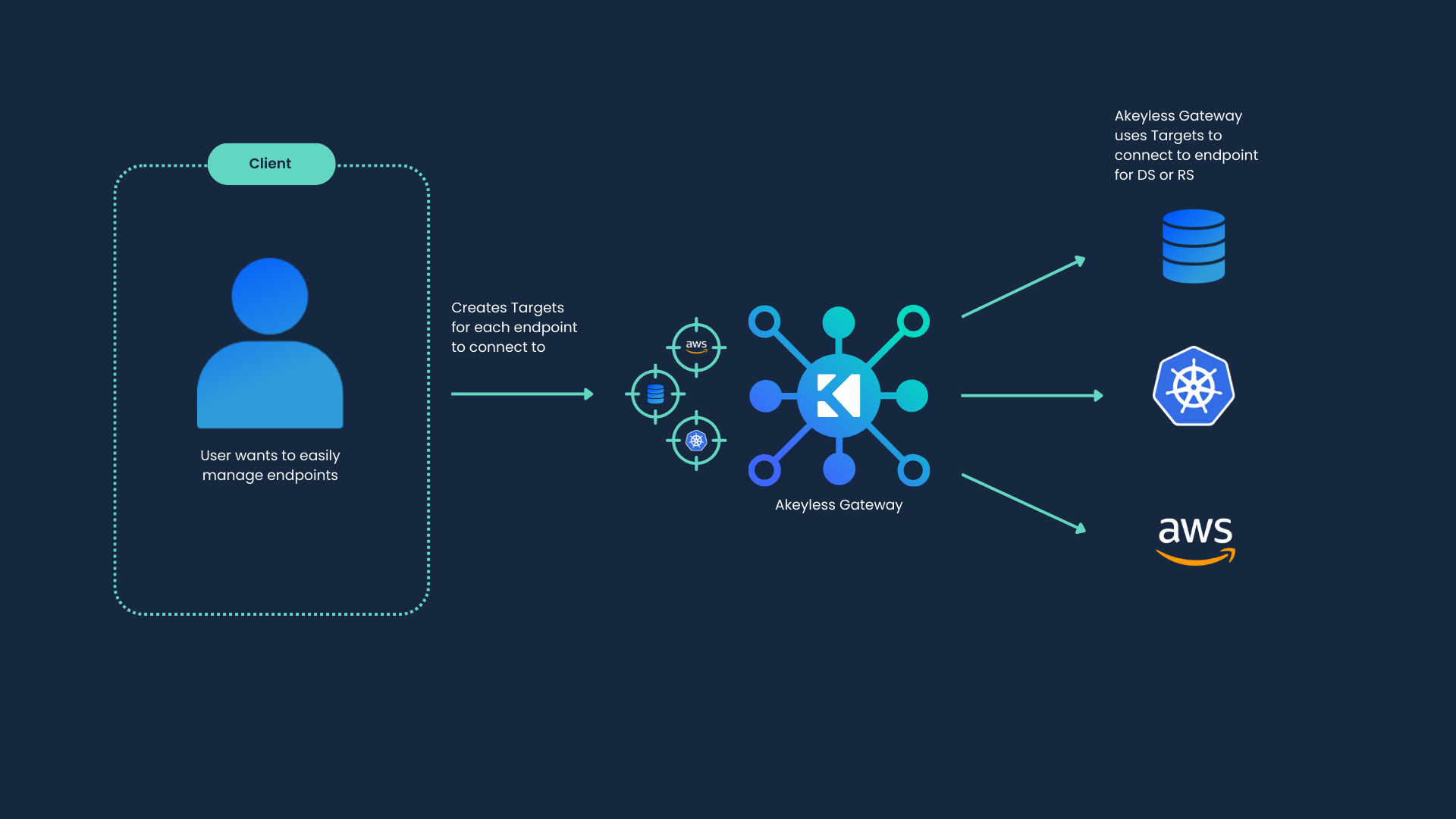
Using targets has three primary advantages:
-
Streamline your creation flow: Creating a target that has the credentials for a specific endpoint will allow you to reference said endpoint in other items like Dynamic Secrets, Rotated Secrets and more, without having to input the details again every time. You can have multiple secrets point to the same Target, making it easy for different teams to connect and minimizing the number of Targets in your organization.
-
Keep your information safe: Using the Role-Based Access Control (RBAC) capabilities, users are not required to have access to, or knowledge of, your privileged account credentials. Simply grant users with
listpermissions on those Target items to provide them with the ability to create Dynamic Secrets or Rotated Secrets. For example, two Database Dynamic Secrets can be created using the same existing Target, but each with its own set of permissions. -
Don't break the credential chain: Targets can also be used to sync encryption keys with an external KMS, or to define a Target to be used with our Rotated Secrets to manage and automate your privilege account credentials rotation. This allows every item referencing the target to be up to date on the necessary information and to stay usable even after rotations are done.
Common Target Families
If you are looking for a specific target type, start with the family that matches your endpoint:
- Database Targets for database credentials that applications and teams reuse across secrets.
- Cloud provider targets: AWS Targets, Azure Targets, and GCP Targets for cloud platform credentials and cloud-specific integrations.
- Certificate automation targets: Let's Encrypt Target, DigiCert Target, Google CA Target, and Cloudflare Target for DNS-01 validation with public Certificate Authority (CA) targets.
- SSH Targets and Web Targets for server access and web-facing endpoints.
Delete protection for targets
Targets support delete protection to reduce accidental deletion risk.
Use the delete protection setting on target create and update operations to help prevent accidental deletion.
For related item protection controls, see Secret and Target Locking.
Tutorial
Check out our tutorial video on Creating and Configuring Targets.
Updated 10 days ago
