API Key
This page discusses creating and using an API key-based authentication method in Akeyless.
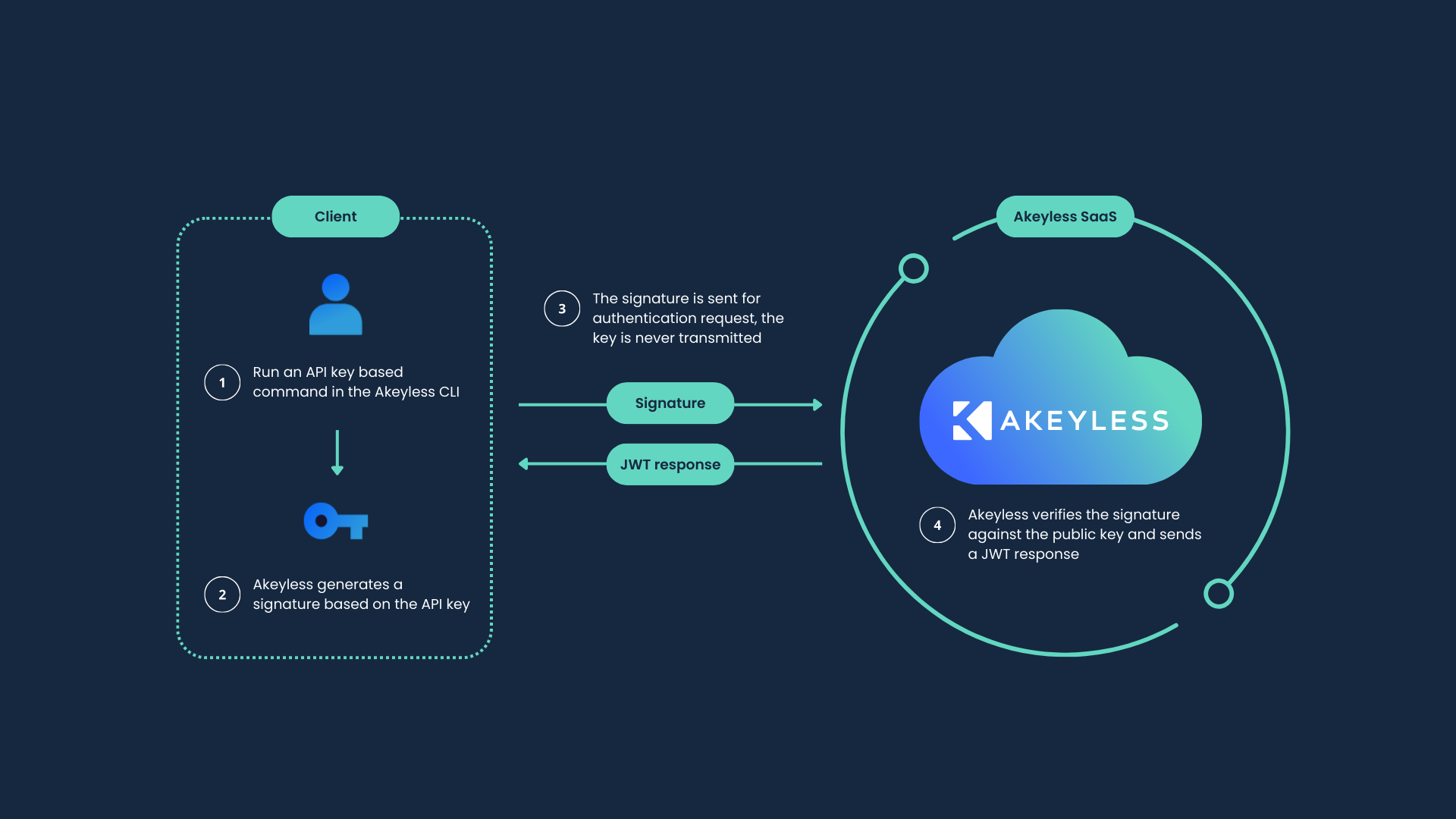
API key authentication allows users and workloads to authenticate to Akeyless using an Access ID and Access Key pair. It is typically used for CLI, SDK, and automation workflows.
API key authentication is intended for programmatic access and is not recommended for direct interactive Console sign-in.
Note:The API Key Authentication Method is not recommended for production use. It works well for getting started with Akeyless, quick proofs of concept (POCs), and other temporary scenarios.
Creating an API Key Authentication Method
API key authentication is available by default for Akeyless accounts. No additional configuration is required.
This action is distinct from creating a new Akeyless account: it creates an additional API key-based authentication method for an existing account.
Creating an API Key Authentication Method with the Console
To create a new API key-based authentication method with the Console:
- In the Console, under Administration, navigate to Users & Auth Methods.
- Select + New. This opens the Create Authentication Method form.
- On the Type selection screen, select API Key, then Next →.
- Enter a name for the Authentication Method in the Name field. Optionally, include a path using
/separators to place the Authentication Method in a virtual folder, then select Finish. - Download the generated CSV file that includes the Access ID and Access Key. Save it in a secure location. This is the last time this access key will be available to view or download.
The Access Key is displayed only once. Store it securely. However, you can reset the access key at any time.
Creating an API Key Authentication Method with the CLI
To create an API key-based authentication method with the CLI:
akeyless auth-method create api-key \
--name <API Key Auth Method Name>The command returns credentials for the new authentication method. The Access Key is displayed only once. Store it securely. Be sure to associate the API key authentication method with one or more Roles.
Read about more parameters available when creating an API key-based authentication method.
Using an API Key Authentication Method
Using an API Key Authentication Method with the Console
To use an API key-based authentication method with the Console:
- Open the Akeyless Console: https://console.akeyless.io.
- In the Or continue with section, select Access Key.
- Enter the Access ID and Access Key, then select Sign in.
Using an API Key Authentication Method with the CLI
To use an API key-based authentication method with a CLI profile, run the Akeyless configure command. For more information about profiles, see CLI Profiles:
akeyless configure \
--profile default \
--access-id <Access ID> \
--access-key <Access Key>To authenticate with an Access ID and Access Key using the CLI, run the Akeyless auth command:
akeyless auth \
--access-type access_key \
--access-id <Access ID> \
--access-key <Access Key>Associate with Access Roles
After creating the authentication method, associate it with one or more Access Roles so authenticated identities can perform actions in Akeyless.
- In the Console, under Administration, navigate to Users & Auth Methods.
- Select the API key authentication method.
- Add the required Access Roles.
- Save the changes.
For role configuration details, see Access Roles.
Update an Existing API Key Authentication Method
API key authentication methods can require updates over time, for example when rotating credentials or changing method-level settings.
To update in the Console:
- In the Console, under Administration, navigate to Users & Auth Methods.
- Select the API key authentication method to update.
- Update the required fields.
- Save the changes.
For CLI update flags, see CLI Reference - Authentication.
Troubleshooting
If API key authentication fails, check the following:
- The Access ID and Access Key are from the same authentication method.
- The Access Key has not been rotated since the credential was stored.
- The authentication method is associated with the required Access Roles.
- The CLI profile is configured with the intended authentication method credentials.
Optional Features
For optional features that apply across Authentication Methods, see Common Optional Features.
Reset Access Key
To reset the Access Key for an existing API key-based authentication method with the Console:
- In the Console, under Administration, navigate to Users & Auth Methods.
- Select the API key authentication method name. The details sidebar opens.
- In the default General tab, select Reset Access Key.
- In the confirmation window, enter the authentication method name, then select Reset Access Key.
To reset the Access Key with the CLI, run the Akeyless reset-access-key command:
akeyless reset-access-key \
--name <API Key Auth Method Name>Updated 18 days ago
Make sure to associate your new Authentication Method with an Access Role to grant the relevant permissions within Akeyless.
