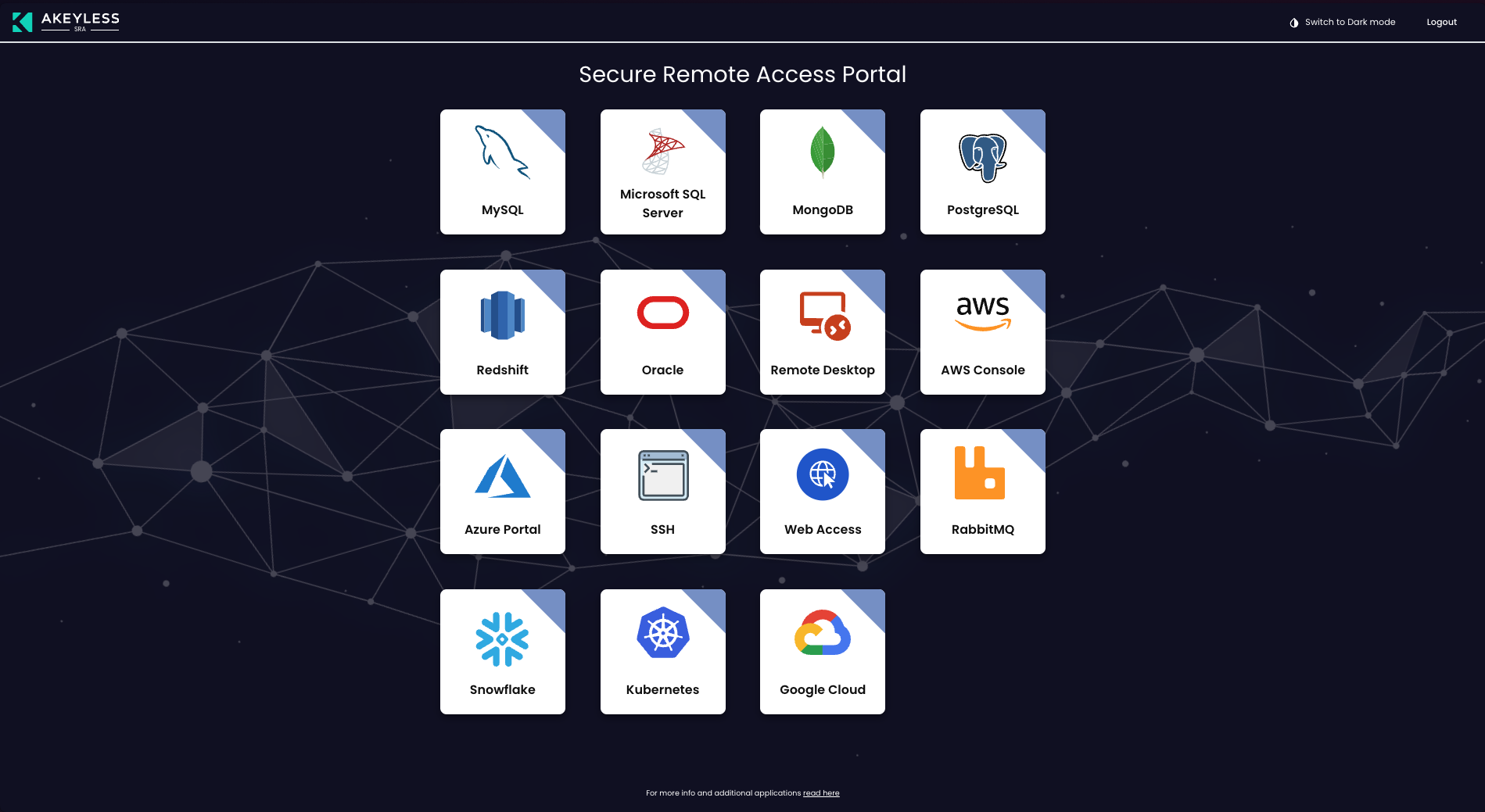
Secure Remote Access Portal
The Secure Remote Access Portal is available through the main console at http://Your-Akeyless-Gateway-URL:8000/sra/portal or through the public SaaS console at https://zerotrust.akeyless.io.
All Akeyless-supported resource types can be accessed using the SRA Portal, CLI, or the Desktop Application.
Currently, the SRA Portal supports the following authentication methods:
Tip (Allowed redirect URL): If you are using SAML or OIDC auth methods, ensure your Gateway URL is trusted.
Connect from the Secure Remote Access Portal
- Open the SRA Portal:
http://Your-Akeyless-Gateway-URL:8000/sra/portal - Select the relevant authentication method. The default is SAML. Enter your SAML Access ID, or choose a different method.
- If you are also working with Zero Trust Web Access, set the Web Application Dispatcher with the external URL of your dispatcher service on port
9000. If you are working with Secure Proxy, also set the Web Proxy URL using port19414. For instructions on how to retrieve these URLs from your cluster, see Get the Dispatcher Service URL. - Click the Generate SAML Bookmark URL to create a link to the completed form. The link is copied to your clipboard for you to save in a convenient place, such as your browser bookmarks, and use in the future to automatically complete the login details.
- Click Sign in.
The portal shows all the resource types that you are authorized to access.
Add a Custom Target for SSH or RDP
In addition to existing hosts that are part of the allowed hosts on the SSH Cert Issuer, you can add new hostnames or IP addresses on the fly by using a matching SSH Cert Issuer that can provide access.
Note (Key Features):
- On-the-Fly Connections: Users can provide a hostname or IP address for RDP or SSH sessions as needed.
- Temporary Host Addition: Hostnames added through this feature are temporary and stored in the browser’s cache.
- Edit and Delete Capability: Users can edit or remove the last added host from the list.
- In the SSH or RDP window, choose Custom Target and click the + button.
- Select the Permission Profile. For example, SSH Cert Issuer.
- Enter Hostname or IP Address.
- Select Confirm.
Users can Edit or Delete the last added host, and it will be removed from the list of hosts in the portal.
Updated 11 days ago
