Secure Remote Access
What Is Secure Remote Access?
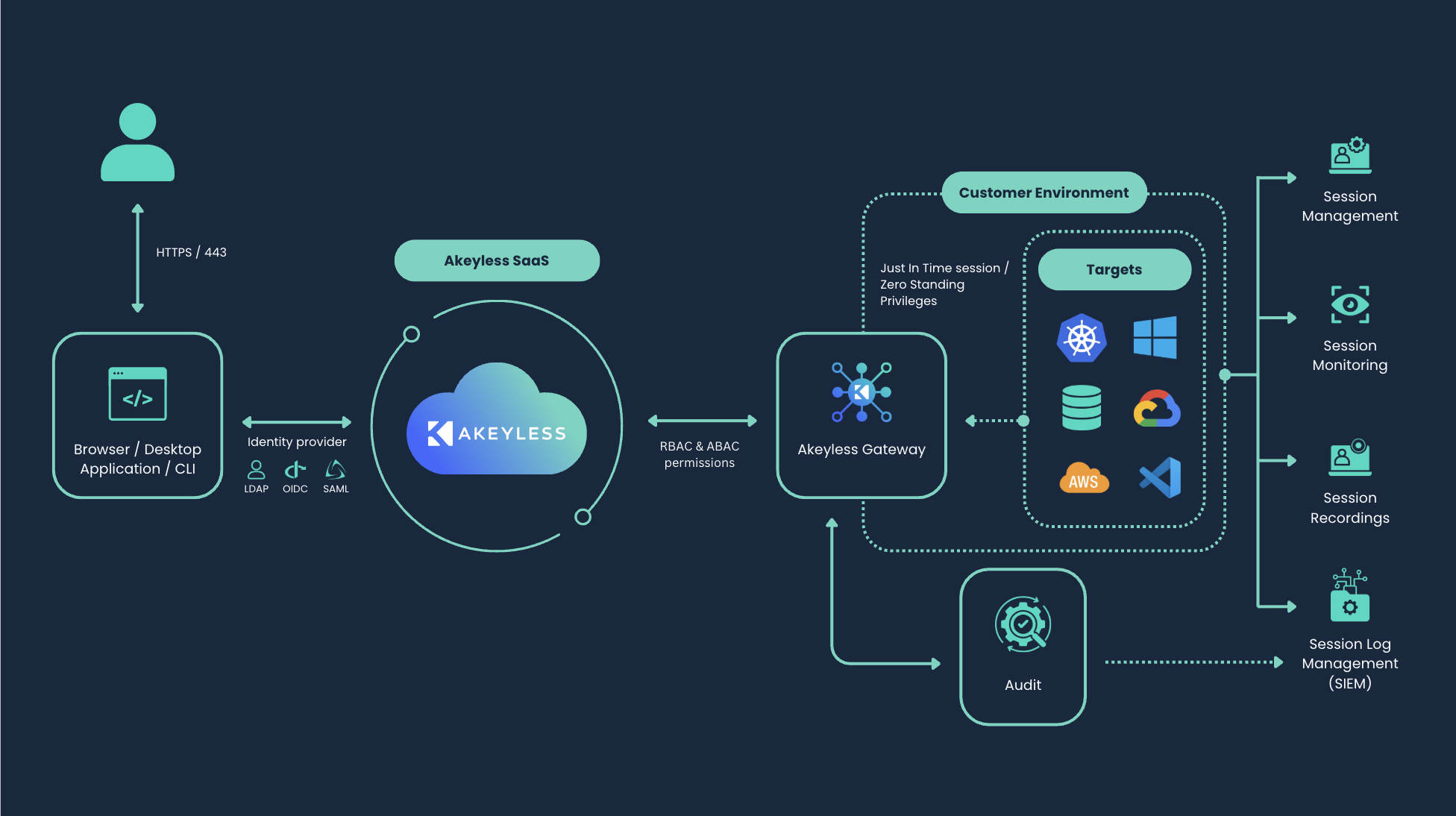
Secure Remote Access (SRA) is part of the Akeyless identity security platform. It provides Zero Trust access to private resources by brokering access through gateway and SRA services with dynamic and rotated secret patterns, rather than long-lived static credentials. This model follows a Zero Standing Privileges (ZSP) approach by minimizing persistent credentials in access flows.
SRA supports interactive access to servers, databases, Kubernetes clusters, web applications, and cloud consoles. Users can connect from the Gateway-hosted portal, the public SRA Portal, the desktop application, or CLI tools such as Akeyless Connect and Akeyless SCP.
Supported access patterns include SSH, RDP, SQL, kubectl, LDAP, and web access workflows.
Note (Getting started):To deploy quickly, start with the Quick Start. For deployment planning and architecture decisions, continue with Setup Overview.
How It Works
At a high level, SRA follows this flow:
- A user authenticates with a configured identity provider.
- Configured SRA access restrictions and policy settings, such as allowed access IDs and authentication controls, are applied through gateway and SRA components, and traffic is routed to SRA services.
- The session is established through SRA web or SSH bastion components.
In gateway-managed deployments, SRA runtime and management paths include:
/sra/portal/sra/web-client/sra/ssh-config/config/sra
These paths are part of the gateway route and SRA configuration model described in the implementation.
Architecture
SRA is deployed with the Akeyless Gateway. Core components are:
- Gateway service for routing and configuration management.
- SSH bastion service for terminal and CLI-native access.
- Web bastion service for browser-based sessions.
- Optional cache and optional Zero Trust Web Access components, depending on topology.
Deployment Models
SRA supports multiple deployment patterns:
- Unified deployment: Deploy SRA by using the
akeyless-gatewaychart with SRA enabled. - Legacy split deployment: Existing environments might still use the standalone SRA chart model, but migration to unified deployment is recommended.
- Topology variants: Kubernetes and Docker Compose are both supported, including Zero Trust Web Access patterns for browser-isolated access.
Important (Migration):New deployments should use unified deployment with the
akeyless-gatewaychart. Existing split deployments should plan migration to reduce operational drift.
Before Deployment
Before deployment, confirm these prerequisites:
- A supported runtime (Kubernetes or Docker Compose).
- Required network access and open ports for gateway and SRA components.
- At least one authentication method, an access role, and an SSH certificate issuer for SSH-based access.
Start Here by Goal
Use this path based on the immediate objective:
- Baseline deployment: Quick Start
- Deployment planning and architecture: Setup Overview
- Resource onboarding: Supported Resource Types
- User operation model: SRA User Guides
- Admin controls and policies: SRA Admin Guides
Documentation Map
Use this map to move through the SRA documentation by workflow:
- Setup and deployment: Setup Overview
- Access configuration and policy controls: SRA Admin Guides
- User access flows (portal, desktop app, and CLI): SRA User Guides
- Session operations and monitoring: Session Management
- Integrations and automation (CLI and API references): CLI Gateway Reference and Akeyless API v2 Reference
- Infrastructure planning and troubleshooting: SRA Setup on Kubernetes and SRA Setup on Docker
What to Configure Next
After baseline deployment, most teams configure these in order:
- Access and entitlement policy for SRA users.
- Session recording and forwarding destination settings.
- Resource-specific access configuration for required target types.
- CLI and API workflows for automation.
Supported Resource Types
The Akeyless Remote Access solution supports connections to the following resource types:
- Databases
- Windows Remote Desktop
- AWS Console
- Azure Portal
- GCP Portal
- SSH Servers
- LDAP Servers
- RabbitMQ
- Kubernetes
- Web Applications
- kubectl
Web Access
Remote access to external software as a service systems can also be configured through the Web Access Application. This supports browser-isolated access to approved web destinations and secure proxy mode for internal resources.
For details about the different remote access components, see Setup Overview.
Updated 14 days ago
